Kindly fill up the following to try out our sandbox experience. We will get back to you at the earliest.
Best Practices for Secure Data Collaboration in Modern Data Stacks
Explore best practices for secure data collaboration to protect sensitive information effectively.

Introduction
In an era where data breaches are increasingly common, secure data collaboration has become essential for organizations aiming to protect sensitive information. Secure data collaboration is essential for organizations seeking to protect sensitive information and facilitate effective information sharing. With the rise in data breaches and regulatory scrutiny, the demand for robust strategies to ensure compliance and protect data integrity is at an all-time high.
Organizations must develop strategies that effectively balance secure collaboration with the need for innovation and stakeholder trust. This article explores best practices and emerging technologies that enable organizations to achieve secure data collaboration while addressing associated challenges. Without a commitment to secure collaboration, organizations may find themselves vulnerable to breaches that could undermine their credibility and operational integrity.
Define Secure Data Collaboration and Its Importance
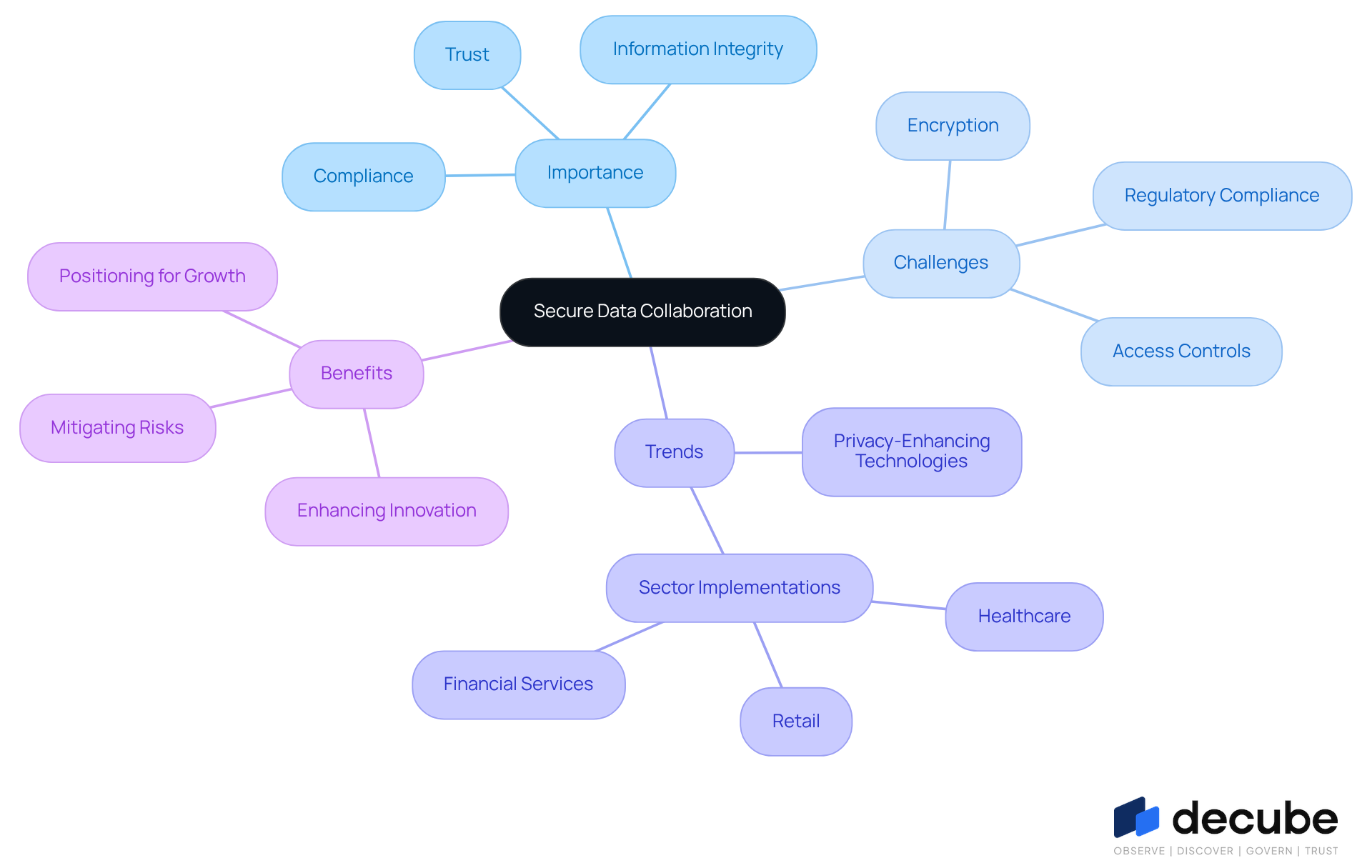
[Secure data collaboration](https://decube.io/post/best-practices-for-your-data-dictionary-template-key-strategies) is critical for organizations aiming to protect sensitive data while facilitating [effective information sharing](https://decube.io/post/10-essential-data-pipeline-observability-solutions-for-engineers). This practice requires overcoming challenges related to encryption, access controls, and [regulatory compliance, including adherence to regulations such as GDPR and HIPAA](https://ibm.com/thought-leadership/institute-business-value/en-us/report/data-security). The importance of secure data collaboration lies in its ability to foster trust among stakeholders, enhance information integrity, and ensure compliance with legal obligations. Consequently, organizations that prioritize secure data collaboration are better positioned to succeed and innovate.
Current trends indicate that entities are increasingly adopting privacy-enhancing technologies to facilitate secure collaboration across various platforms without compromising privacy. Successful implementations of secure information sharing have been observed in sectors such as healthcare, where organizations utilize shared clinical information to improve patient outcomes while adhering to stringent regulations.
Ultimately, organizations that invest in secure information sharing not only mitigate risks but also position themselves for future growth and innovation.
Understand Compliance Requirements for Data Sharing
Organizations face increasing challenges in navigating a complex landscape of compliance obligations, particularly with the evolving regulations surrounding information sharing. The General Data Protection Regulation (GDPR) imposes stringent guidelines for handling personal information, emphasizing the need for transparency, consent, and protection measures. At the same time, HIPAA regulates health information sharing, balancing patient privacy with the need for essential healthcare exchanges. Moreover, frameworks like SOC 2 and ISO 27001 provide vital standards for managing information security and privacy, underscoring the significance of strong governance practices.
Starting in 2026, organizations need to be vigilant in adapting to new regulatory changes, particularly state privacy laws that complicate information sharing. For instance, the introduction of extensive privacy regulations in states such as Indiana, Kentucky, and Rhode Island will require businesses to reevaluate their adherence strategies and execution timelines. Non-compliance can lead to severe penalties, with statistics indicating that over 747 significant breaches occurred in 2023, impacting more than 168 million records. This underscores the need for organizations to proactively integrate compliance into their information governance frameworks.
Experts advise that organizations shouldn’t wait for enforcement actions to prompt compliance efforts. Proactive evaluations and updates are essential to mitigate risks associated with information sharing. As one specialist noted, "Organizations that wait for enforcement letters to stimulate action will encounter not only penalties but also the operational disruption of implementing regulatory programs while under scrutiny from authorities." Thus, integrating adherence into information management practices is not only a legal requirement but a strategic necessity for sustaining trust and operational integrity.
Decube's automated crawling feature enhances information observability and governance by ensuring that metadata is effortlessly managed and kept current. This feature enables organizations to control who can access or modify information, simplifying the approval process required for compliance. Furthermore, the importance of information lineage in regulatory adherence cannot be overstated. By providing insight into information origins, transformations, and access, Decube's automated lineage tools assist enterprises in demonstrating compliance and minimizing risk. These tools address common challenges such as siloed systems and incomplete metadata, ensuring that compliance strategies are robust and effective.

Implement Best Practices for Secure Data Collaboration
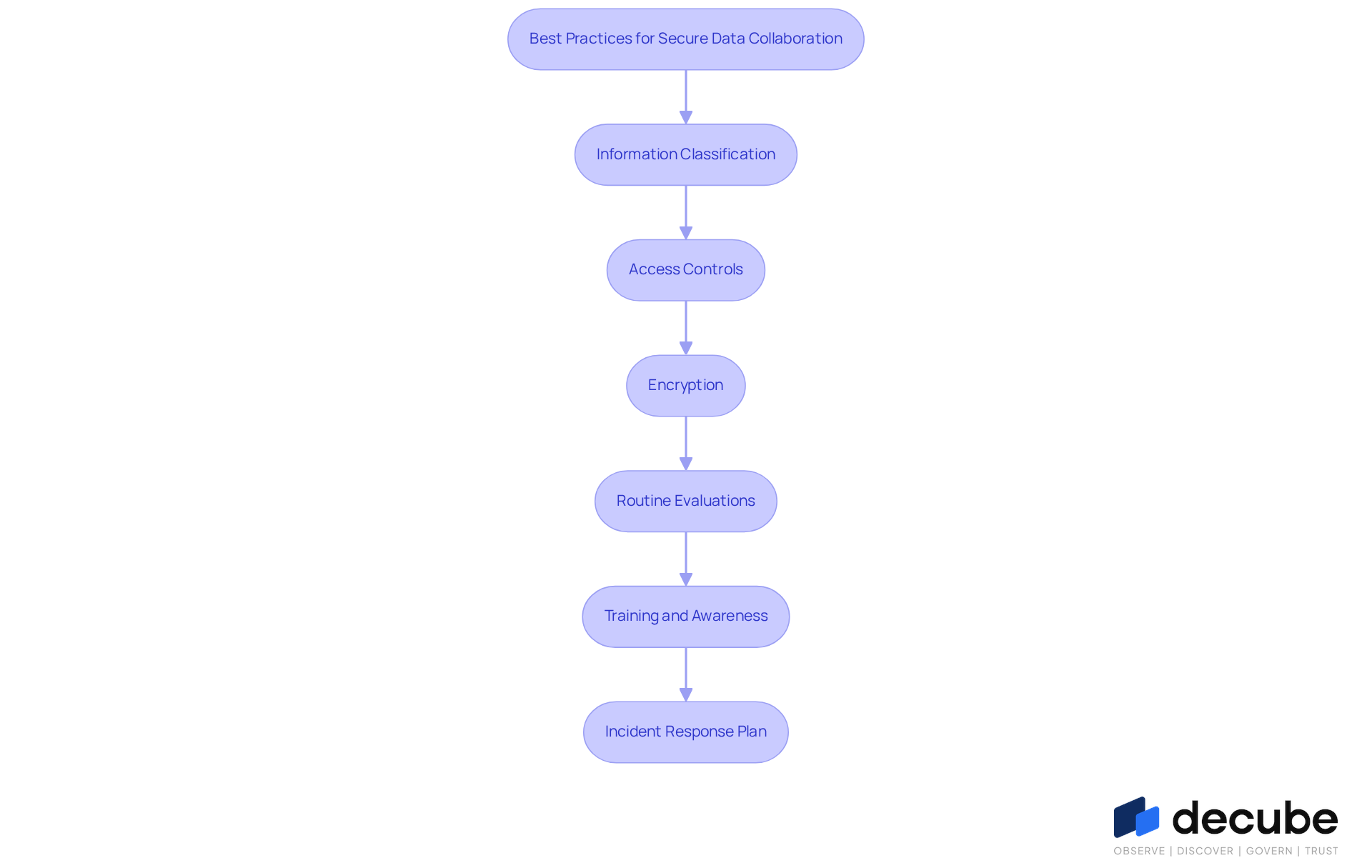
In an increasingly interconnected world, the risks associated with data collaboration are more pronounced than ever. To ensure secure data collaboration, organizations should adopt the following best practices:
- Information Classification: Categorizing information according to sensitivity is crucial for establishing suitable protective measures. This practice enables organizations to apply the appropriate level of protection tailored to various information types, thereby enhancing overall security.
- Access Controls: Implementing strict access controls is vital to ensure that only authorized personnel can access sensitive information. Role-based access controls (RBAC) are especially effective, as they restrict information exposure based on user roles, significantly lowering the risk of unauthorized access.
- Encryption: Utilizing encryption for information both at rest and in transit is crucial for keeping data confidential and intact. This step is essential for safeguarding sensitive content from unauthorized access, especially in an era where data breaches are increasingly common.
- Routine Evaluations: Regular audits help organizations spot weaknesses in their data-sharing practices. Proactively addressing these vulnerabilities is essential for maintaining a strong defense posture.
- Training and Awareness: Informing staff about information protection best practices is essential. Consistent training sessions can strengthen a culture of security within the organization, ensuring that all team members comprehend their role in safeguarding sensitive information.
- Incident Response Plan: Creating and upkeeping an incident response plan is essential for tackling potential breaches promptly and efficiently. This plan minimizes damage and ensures compliance with legal obligations, which is increasingly important in the evolving regulatory landscape of 2026. Neglecting these best practices could lead to severe consequences, such as data breaches and regulatory penalties, which can compromise secure data collaboration.
Leverage Technology for Enhanced Data Security and Efficiency
Organizations often struggle to protect sensitive information while achieving secure data collaboration. To address these challenges, they can implement various technologies that enhance data security and streamline their collaborative efforts:
- Information Encryption Tools: Implement encryption solutions that provide end-to-end encryption for sharing, ensuring that sensitive details remain secure throughout their lifecycle.
- Secure File Sharing Platforms: It's essential to use secure file sharing solutions that come with features like access controls, audit trails, and loss prevention (DLP) capabilities to keep confidential information safe.
- Collaboration Software: Adopt collaboration tools that incorporate protective features, including secure messaging and file sharing, to facilitate safe communication among team members.
- Data Governance Platforms: Invest in governance solutions that offer insight into information lineage, adherence tracking, and policy management, allowing entities to maintain control over their assets.
- AI and Machine Learning: Utilize AI and machine learning technologies to automate information monitoring and anomaly detection, enabling organizations to recognize and react to potential threats in real-time.
- Cloud Security Solutions: Embrace cloud security solutions that deliver robust protection for data stored in the cloud, ensuring compliance with industry standards and safeguarding against unauthorized access.
By adopting these technologies, organizations can achieve secure data collaboration, safeguarding their data while streamlining their collaborative efforts, ultimately leading to improved outcomes.

Conclusion
In an era where data breaches are increasingly common, secure data collaboration is vital for organizations aiming to protect sensitive information while facilitating effective information sharing. Organizations face significant challenges in navigating compliance complexities and implementing effective security measures, which are essential for fostering trust and ensuring legal adherence. Prioritizing secure data collaboration not only reduces potential risks but also enables organizations to innovate and thrive in a rapidly evolving data landscape.
This article has outlined several key strategies for achieving secure data collaboration. These include:
- Understanding compliance requirements
- Implementing best practices such as information classification and access controls
- Leveraging advanced technologies like encryption and AI
By addressing these aspects, organizations can create a secure environment that safeguards sensitive data and promotes efficient collaboration across teams and platforms.
As regulations evolve, the need for secure data collaboration becomes increasingly critical. Organizations must proactively approach compliance and security by integrating best practices and innovative technologies into their data-sharing frameworks. This approach not only safeguards valuable assets but also strengthens operational integrity and cultivates a security-focused culture that drives future success.
Frequently Asked Questions
What is secure data collaboration?
Secure data collaboration is the practice of protecting sensitive data while enabling effective information sharing among organizations.
Why is secure data collaboration important?
It is important because it fosters trust among stakeholders, enhances information integrity, and ensures compliance with legal obligations, thereby positioning organizations for success and innovation.
What challenges do organizations face in secure data collaboration?
Organizations face challenges related to encryption, access controls, and regulatory compliance, including adherence to regulations such as GDPR and HIPAA.
What are current trends in secure data collaboration?
Current trends indicate that organizations are increasingly adopting privacy-enhancing technologies to facilitate secure collaboration across various platforms without compromising privacy.
In which sectors has secure information sharing been successfully implemented?
Secure information sharing has been successfully implemented in sectors such as healthcare, where organizations use shared clinical information to improve patient outcomes while adhering to stringent regulations.
How does investing in secure information sharing benefit organizations?
Investing in secure information sharing helps organizations mitigate risks and positions them for future growth and innovation.
List of Sources
- Define Secure Data Collaboration and Its Importance
- Quotes Related to Data and Data Governance (https://blog.idatainc.com/quotes-related-to-data-and-data-governance)
- Data security as business accelerator? (https://ibm.com/thought-leadership/institute-business-value/en-us/report/data-security)
- Secure Data Sharing: The Complete Guide to Modern Data Collaboration (https://databricks.com/blog/secure-data-sharing-complete-guide-modern-data-collaboration)
- Data Privacy Quotes: Leaders on Importance of Data Ownership | Mbaindiguim Edgar posted on the topic | LinkedIn (https://linkedin.com/posts/mbaindiguimedgar_7-meaningful-quotes-about-data-privacy-activity-7422254718401474561-_2pL)
- 20 Quotes Proving The Need for Security Integrations (https://synqly.com/moving-from-ok-to-best-in-class-20-quotes-from-experts-proving-the-need-for-security-integrations)
- Understand Compliance Requirements for Data Sharing
- 2026 Healthcare Privacy Regulations: What’s New and How to Stay Compliant (https://accountablehq.com/post/2026-healthcare-privacy-regulations-what-s-new-and-how-to-stay-compliant)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- 2026 U.S. Data Privacy Developments: New and Amended Laws (https://gunster.com/newsroom/publications/2026-data-privacy-laws-state-changes-universal-opt-out-compliance)
- Privacy Laws Ring in the New Year: State Requirements Expand Across the U.S. in 2026 (https://bakerdonelson.com/privacy-laws-ring-in-the-new-year-state-requirements-expand-across-the-us-in-2026)
- New year, new rules: US state privacy requirements coming online as 2026 begins | IAPP (https://iapp.org/news/a/new-year-new-rules-us-state-privacy-requirements-coming-online-as-2026-begins)
- Implement Best Practices for Secure Data Collaboration
- How to Prevent Data Breaches in 2026: Security Best Practices (https://soti.net/resources/blog/2026/how-to-prevent-data-breaches-in-2026-security-best-practices)
- Data Privacy Governance: 8 Best Practices (2026) (https://cdp.com/articles/data-privacy-governance-best-practices)
- How 2026 Will Reshape Data Privacy and Cybersecurity (https://founderslegal.com/how-2026-will-reshape-data-privacy-and-cybersecurity)
- Data Protection Strategies for 2026 (https://hyperproof.io/resource/data-protection-strategies-for-2026)
- Access Control Statistics: Trends & Insights (https://entrycare.com/access-control-statistics)
- Leverage Technology for Enhanced Data Security and Efficiency
- AI in 2026: Experts Reveal the Next Era of Security, Collaboration & Innovation (https://cyware.com/news-and-press/ai-in-2026-experts-reveal-the-next-era-of-security-collaboration-and)
- 9 AI Cybersecurity Trends to Watch in 2026 (https://sentinelone.com/cybersecurity-101/data-and-ai/ai-cybersecurity-trends)
- Secure File Transfer Market (https://market.us/report/secure-file-transfer-market)
- Data Protection Strategies for 2026 (https://hyperproof.io/resource/data-protection-strategies-for-2026)
- The State of AI Cybersecurity 2026 (https://darktrace.com/resource/the-state-of-ai-cybersecurity-2026)

_For%20light%20backgrounds.svg)