Kindly fill up the following to try out our sandbox experience. We will get back to you at the earliest.
Master Managed Data Security: Best Practices for Data Engineers
Explore best practices for managed data security to protect sensitive information effectively.

Introduction
The rise in cyber threats, especially ransomware attacks, highlights the urgent need for effective data security management within organizations. Data engineers are tasked with the complex responsibility of protecting sensitive information while adhering to a multitude of industry regulations. This article explores best practices for data security management, emphasizing key strategies and frameworks that not only safeguard organizational assets but also strengthen resilience against emerging threats.
How can data engineers successfully implement these practices to reduce risks and enhance their organizations' security posture?
Define Data Security Management and Its Importance
encompasses comprehensive policies, procedures, and technologies that organizations implement to safeguard their information against unauthorized access, corruption, or theft throughout its lifecycle. This management is crucial for maintaining - collectively known as the CIA triad. Given that ransomware attacks have surged fourfold since 2021, the importance of robust security practices cannot be overstated. Breaches not only jeopardize sensitive information but can also result in significant financial losses and reputational damage.
For engineers, the responsibility of information protection extends beyond mere safeguarding; it includes ensuring compliance with such as:
- HIPAA
- GDPR
Adhering to these standards is vital for fostering trust among stakeholders and customers, particularly as organizations navigate an increasingly complex cybersecurity landscape. Ongoing monitoring and automated strategies are becoming indispensable, allowing organizations to assess risks swiftly and maintain visibility into information access and sharing.
Decube's unified information trust platform enhances this visibility through its automated , which not only illustrates the complete information flow across components but also directly contributes to by ensuring accuracy and compliance. Additionally, Decube's , including user-controlled metadata storage and retention, provide further assurance of integrity. As John Grancarich, Chief Strategy Officer, emphasizes, "Visibility will become the most important priority in cybersecurity." Therefore, incorporating effective information protection practices, supported by Decube's advanced observability and governance features, is essential for safeguarding organizational assets and ensuring operational resilience.

Identify Key Components and Frameworks for Data Security Management
Effective information protection management hinges on several key components: classification, , encryption, and . Frameworks such as the and ISO/IEC 27001 provide structured methodologies for the efficient implementation of these components.
is essential, as it involves categorizing information based on its sensitivity, which guides the application of appropriate security measures. are critical for ensuring that only authorized personnel can access sensitive information, thereby mitigating the risk of unauthorized access. , safeguarding information both at rest and in transit, thus ensuring confidentiality and integrity.
Monitoring tools, including Decube's and preset field monitors, are vital in identifying unauthorized access attempts and potential breaches. These tools enable entities to respond swiftly to incidents. By leveraging these elements alongside established frameworks, engineers can cultivate a robust protective posture that not only diminishes risks but also .
For instance, adopting the NIST CSF can significantly reduce cybersecurity risks and bolster organizational resilience. In 2026, entities that embraced the CSF reported enhanced communication and collaboration, which are crucial for effective cybersecurity oversight. Furthermore, the framework's emphasis on aligns well with evolving regulatory demands, making it a preferred choice for organizations aiming to strengthen their .

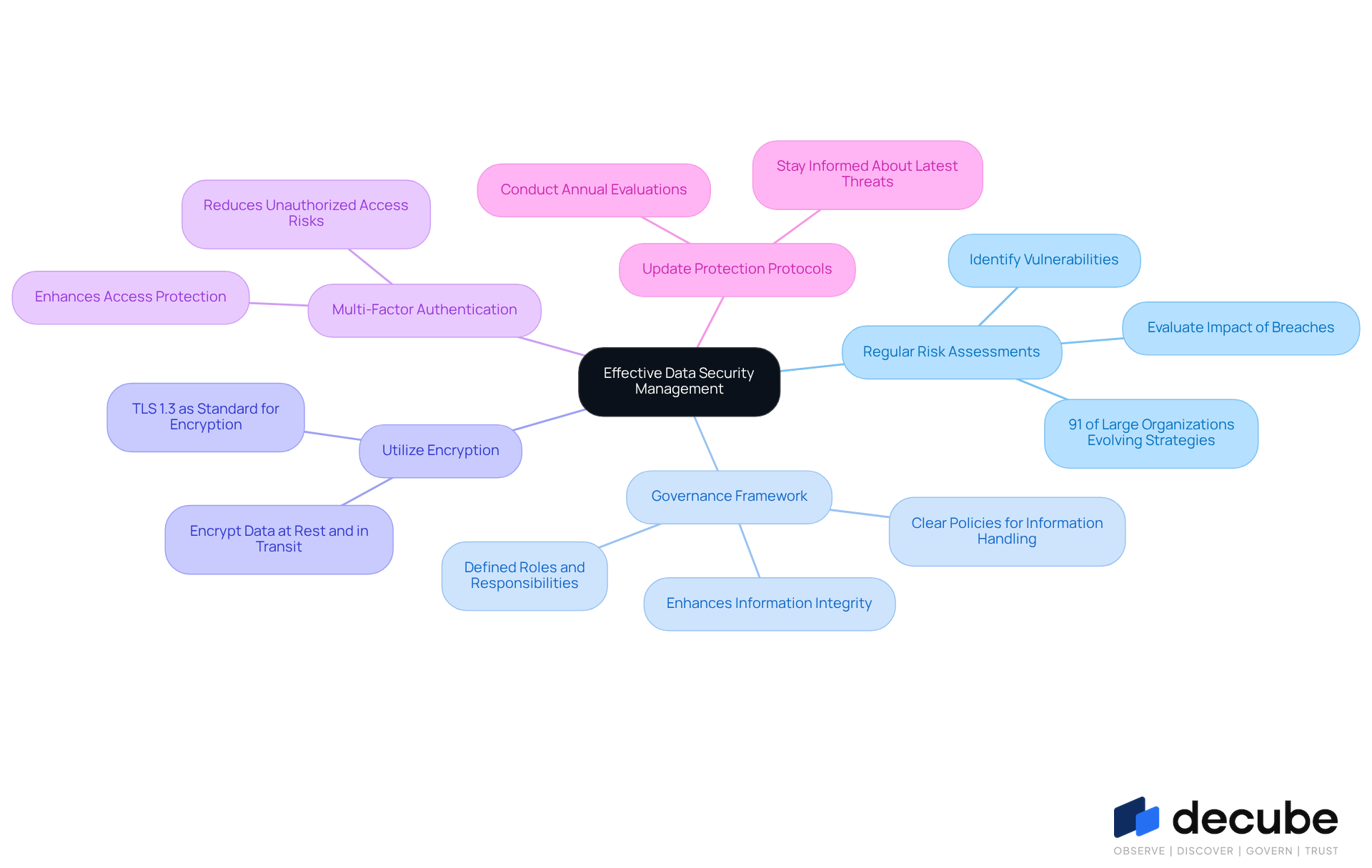
Implement Best Practices for Effective Data Security Management
To implement effective data security management, data engineers should adopt several best practices:
- Conduct Regular Risk Assessments: and evaluating the potential impact of data breaches. This proactive approach allows organizations to address weaknesses before they can be exploited. Notably, 91% of organizations with over 100,000 employees have evolved their cybersecurity strategies due to geopolitical volatility, underscoring the necessity for continuous evaluation.
- : Developing a robust information governance framework is crucial. This framework should outline clear policies for information handling, access, and sharing, along with defined roles and responsibilities for information stewardship. Effective governance enhances information integrity and ensures adherence to regulatory requirements.
- Utilize Encryption: Encrypting sensitive information both at rest and in transit is vital for protecting it from unauthorized access. is recommended as the contemporary standard for encryption in transit, offering improved protection features that safeguard information during transmission.
- : Enhancing access protection through MFA is a critical measure. By requiring multiple forms of verification before granting access to sensitive information, organizations can significantly reduce the risk of unauthorized access and account compromise.
- : Staying informed about the latest threats and regularly updating protection protocols is essential for mitigating risks. Organizations should to adapt to evolving threats.
By adhering to these best practices, data engineers can significantly enhance their organization's information protection stance, ensuring a robust defense against potential breaches.
Address Common Challenges in Data Security Management
Data security management presents several challenges that data engineers must navigate:
- : As organizations expand, information often becomes fragmented across various platforms, complicating management and security efforts. By 2026, enterprises are projected to utilize an average of 36 different cloud and SaaS providers, exacerbating . Establishing a is crucial to mitigate this issue, ensuring that information remains accessible and manageable. Decube's automated crawling feature not only updates metadata but also provides a comprehensive perspective of assets, enhancing oversight and control. As David Tairych observes, " occurs when enterprise datasets become disaggregated across various cloud environments, complicating comprehensive information management and limiting correlation possibilities."
- : Employees with access to sensitive information can pose significant risks. Regular training programs and stringent access controls are vital in minimizing these threats. Organizations must recognize that sensitive information frequently transfers between different locations, including inboxes, making effective monitoring and management of access essential. Decube enables organizations to control who can access or modify information through a specified approval process, thereby improving security. Akshay Joshi emphasizes that "87% of leaders view AI-related vulnerabilities as the fastest-growing cyber risk," underscoring the importance of addressing .
- : Keeping pace with evolving regulations such as GDPR and HIPAA can be daunting. Data engineers should remain vigilant regarding compliance requirements and integrate them into their information handling practices. The overlapping nature of state, federal, and international regulations often leads to confusion, necessitating a clear compliance strategy. Understanding is essential, as it illustrates the entire journey of data across various systems-from source to transformation to consumption-helping businesses ensure accuracy and meet compliance requirements, thus fostering trust in their data management practices.
- : Cyber threats are in a constant state of flux, requiring organizations to adapt swiftly. Ransomware attacks have surged fourfold since 2021, highlighting the need for robust protective measures. Regularly updating protection protocols and conducting threat assessments can help organizations remain proactive against potential attacks. By leveraging Decube's automated monitoring and analytics, engineers can enhance their information quality and governance, ensuring readiness for evolving threats.
By understanding and addressing these challenges, data engineers can strengthen their managed data security strategies and safeguard their organizations from potential breaches.

Conclusion
Effective data security management stands as a critical component for organizations seeking to safeguard their information assets in an increasingly complex digital landscape. By implementing comprehensive policies, utilizing advanced technologies, and adhering to industry standards, organizations can significantly bolster their defenses against unauthorized access and data breaches. The alarming rise in cyber threats underscores the importance of robust security practices, making it imperative for data engineers to prioritize data security within their operational strategies.
Key insights from the article emphasize the necessity of:
- Regular risk assessments
- The establishment of a governance framework
- The implementation of encryption and multi-factor authentication as vital best practices for effective data security management
Furthermore, addressing challenges such as:
- Information sprawl
- Insider threats
- Compliance with evolving regulations
is essential for fostering a secure environment. By leveraging structured frameworks like the NIST Cybersecurity Framework, organizations can enhance their resilience and ensure compliance with regulatory demands.
In conclusion, the significance of mastering managed data security cannot be overstated. As cyber threats continue to evolve, organizations must adopt a proactive approach to data protection. By embracing best practices and utilizing advanced tools, data engineers can not only safeguard sensitive information but also build trust with stakeholders and customers. The commitment to effective data security management transcends regulatory requirements; it is a strategic imperative that can determine the long-term success and resilience of an organization in the face of ever-changing threats.
Frequently Asked Questions
What is data security management?
Data security management refers to the comprehensive policies, procedures, and technologies that organizations implement to protect their information from unauthorized access, corruption, or theft throughout its lifecycle.
Why is data security management important?
It is crucial for maintaining confidentiality, integrity, and availability of information, collectively known as the CIA triad. With the increase in ransomware attacks and the potential for financial losses and reputational damage from breaches, robust security practices are essential.
What are the key industry standards for information protection that engineers must comply with?
Engineers must ensure compliance with essential industry standards such as SOC 2, ISO 27001, HIPAA, and GDPR.
How does compliance with industry standards benefit organizations?
Adhering to these standards fosters trust among stakeholders and customers, which is vital in a complex cybersecurity landscape.
What role does ongoing monitoring play in data security management?
Ongoing monitoring and automated strategies are essential for assessing risks swiftly and maintaining visibility into information access and sharing.
How does Decube’s unified information trust platform enhance data security management?
Decube's platform enhances visibility through its automated column-level lineage feature, illustrating the complete information flow across components and contributing to information protection oversight by ensuring accuracy and compliance.
What additional features does Decube provide to ensure integrity in information management?
Decube offers user-controlled metadata storage and retention, which further assures the integrity of information management practices.
What is the significance of visibility in cybersecurity according to John Grancarich?
John Grancarich emphasizes that "Visibility will become the most important priority in cybersecurity," highlighting the need for effective information protection practices supported by advanced observability and governance features.
List of Sources
- Define Data Security Management and Its Importance
- Data Protection Strategies for 2026 & Beyond: A Practical Roadmap (https://securityboulevard.com/2026/03/data-protection-strategies-for-2026-beyond-a-practical-roadmap)
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- Data security is still the most pressing issue for many firms (https://techradar.com/pro/security/data-security-is-still-the-most-pressing-issue-for-many-firms-so-what-can-your-business-do)
- 2026 Cybersecurity Outlook: Why DSPM Will Define the Next Era of Data Protection - vmblog.com (https://vmblog.com/archive/2025/11/05/2026-cybersecurity-outlook-why-dspm-will-define-the-next-era-of-data-protection.aspx)
- Countdown to Data Privacy Day 2026 - What's On the Horizon: 2026 Data Privacy Trends That Will Redefine Compliance (https://bsk.com/news-events-videos/what-39-s-on-the-horizon-2026-data-privacy-trends-that-will-redefine-compliance)
- Identify Key Components and Frameworks for Data Security Management
- Top NIST Best Practices for Enhancing Cyber Resilience in 2026 (https://panorays.com/blog/nist-best-practices)
- NIST compliance in 2026: A complete implementation guide | UpGuard (https://upguard.com/blog/nist-compliance)
- What is the NIST Cybersecurity Framework (CSF)? 2026 Overview (https://strata.io/glossary/nist-cybersecurity-framework-csf)
- Topic: Data security (https://statista.com/topics/13106/data-security?srsltid=AfmBOooTG3BrvcB3HapuFrQBV_hrjGDZZCN3zZ_1XBh3Ym6kPPoA1zgh)
- nextgov.com (https://nextgov.com/cybersecurity/2026/01/nist-releases-new-draft-cybersecurity-framework-systems-never-stop-moving/411074)
- Implement Best Practices for Effective Data Security Management
- Data Protection Strategies for 2026 & Beyond: A Practical Roadmap - Centraleyes (https://centraleyes.com/data-protection-strategies-for-2026-beyond)
- Data Security Best Practices (2026): Practical Controls to Protect Sensitive Data (https://datastealth.io/blogs/data-security-best-practices)
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- How to Prevent Data Breaches in 2026: Security Best Practices (https://soti.net/resources/blog/2026/how-to-prevent-data-breaches-in-2026-security-best-practices)
- Address Common Challenges in Data Security Management
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- Cybersecurity Challenges for Organizations in 2026 - CVG Strategy (https://cvgstrategy.com/cybersecurity-challenges-for-organizations-in-2026)
- What is Data Sprawl? 2026 End to End Guide | Concentric AI (https://concentric.ai/data-is-everywhere-understanding-and-managing-data-sprawl)
- To Overcome Data Sprawl, Use the Right Data Patterns (https://blog.equinix.com/blog/2026/02/19/to-overcome-data-sprawl-use-the-right-data-patterns)
- Top Cybersecurity Challenges to Watch for in 2026 | SWK Technologies (https://swktech.com/top-cybersecurity-challenges-to-watch-for-in-2026)

_For%20light%20backgrounds.svg)